Security refers
to techniques for ensuring that data stored in a computer cannot be read or compromised
by any individuals without authorization. Most security measures involve data encryption
and passwords. Data encryption is the translation of data into a form that is unintelligible
without a deciphering mechanism. A password is a secret word or phrase that gives
a user access to a particular program or system.
· Passive - An attack such
as listening to communications then attacking the encryption scheme off line
may be done.
• Attempt to
learn or make use of information from the system but do not affect system resources
• Two types:
§
Release
of message contents
ex: telephone
conversation, sensitive info in the form of a file, etc.
§
Traffic
analysis
ü
Pattern
analysis
• Difficult to
detect, so emphasis on prevention rather than detection
· Active - A common
attack of this type is the man in the middle attack. During this attack the
attacker may try to convince the victim that they are communicating with
another party when they are really communicating with the attacker. The
attacker may use the attack to gain passwords or other vital information.
• Attempt to modify
data stream or create a false stream.
• Easy to detect
but difficult to prevent.
• Types:
§
Masquerade
- impersonating by replay of valid authentication sequence.
§
Replay
– capture data unit and use it in retransmissions to produce unauthorized
effect.
· Dictionary
attack -
A means attacking a system to determine passwords from hashed or encrypted
passwords.
Impersonating a client is another way for impostors to gain access to
sensitive information stored on a server:
A denial of service (DoS) attacker can flood a network with requests,
with the result that legitimate network users will no longer have access:
An impostor can
gain access to sensitive information by impersonating a legitimate server:
An impostor can
also mount a man-in-the middle attack by simultaneously impersonating both a
legitimate client and a legitimate server.
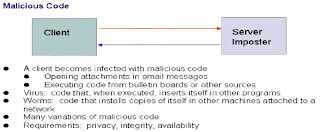
A client machine
can be infected with malicious code, such as a worm or virus, that is downloaded
from an untrustworthy server:
To deal with
these threats, the following security requirements are needed: privacy or
confidentiality,
integrity, authentication, non-repudiation, etc.
1 1)
Confidentiality (the information cannot be
understood by anyone for whom it was unintended)
only
sender, intended receiver should “understand” message contents
– sender
encrypts message, receiver decrypts message
2) Integrity (the
information cannot be altered in storage or transit between sender and intended
receiver without the alteration being detected)
Sender, receiver
want to ensure message not altered (in transit, or afterwards) without detection
3) Non-repudiation
(the creator/sender of the information cannot deny at a later stage his or her
intentions in the creation or transmission of the information)
4) Authentication
(the sender and receiver can confirm each others identity and the origin/destination
of the information)












0 comments